As we enter the thick of budget season, especially in a time where budgets are expected to start tightening, security and IT leaders need to anticipate the discussions they are going to have with executive leaders. This means proactively preparing a formal business case for the security program to ensure funding for upcoming projects.
But, you may be asking yourself, what are the key elements I need to include in my business case in order to “sell” executive leadership on my security program? I recently wrote an article for HelpNet Security talking about specific tips to consider when making a business case for security, but I want to dig a little deeper on the key mechanics of a winning business case.
In my experience as a cybersecurity leader, there are three core sections that you need to keep in mind when it comes to crafting a winning business case:
- Current situation and strategic opportunity
- Financial highlights
- Recommended alternative
WIth those elements in mind, I will give you a quick rundown of how each of these core sections should function in your business case.
Current situation and strategic opportunity
First, outline the current situation and strategic opportunity. This is your chance, through a written dialogue, to relay the importance and benefits of your project. It should be concise, hard hitting, and include current metrics. If there are customers that require this or information on your competitors’ capabilities, this would be the time to mention it.
Outline the key assumptions that you have made during the building of this business case. For example, these assumptions include resources in the IT team or other groups that will be available as needed to assist in the deployment, or if the organization will continue to grow through M&A. Although, be careful to not make an assumption that, if not true, will completely negate your business case. For instance, if you say that you assume that your organization will continue to grow through M&A and the business does not have any plans for M&A, then unless you only need the new service for that one purpose, I would not state that as an assumption, as they may not approve the project based on the M&A assumption.
You will also want to describe the vision of the new service as it relates to the business. How does the project provide business value and what are the expected outcomes? The outcomes will be your measure of success after the project is complete. There should be clear indication of the metrics that you will use to measure the success. Always be careful if part of your business case is to decommission a prior service, so you allow time to complete the decommissioning. All too often the decommission is delayed or sometimes not done at all, which then leads to higher than expected costs.
Financial highlights
Once you have described the project, benefits, and outcomes, now it is time to lay out the financial picture of the recommended solution. It’s good to start this off by answering big questions, such as:
- What are the requirements for personnel?
- What support teams do you need?
- What are the capital requirements and operating expense costs?
- What savings do you expect after the project is complete?
In this section you want to be very clear about the benefits and costs. Post implementation this is where the review team will focus on whether you delivered on the benefits, if the cost was in line with what was promised, and if the new service is fully functional for all of the business.
Include the hard financial analysis, as appropriate, such as return on investment (ROI), total cost of ownership (TOC), net present value (NPV), internal rate of return (IRR), and the computations that back up your analysis. In most security projects you won’t have NPV or IRR calculations.
There are often benefits and costs that are not covered as part of the financial calculations such as soft costs and side benefits. A short description of those benefits, such as increased efficiency, regulatory compliance, etc., is appropriate at this point. It is good to mention those, but don’t rely on them as your cost justification.
Recommended alternative
Now that you have laid out the current situation, the opportunity for improvement, and the financial analysis, now it is time to describe the suggested alternative. Describe the solution and the vendor that will be used. If you plan to have consulting services to help get the product running or perform ongoing maintenance, include this in the description and the financial analysis. You will also want to discuss the threat and risks to the project’s success, as well as controls and security processes that will be implemented as part of the project.
Provide a brief outline of the process used to select the recommended solution. How was the list of competitors created? How did you select the final providers? Did you do a proof of value test?
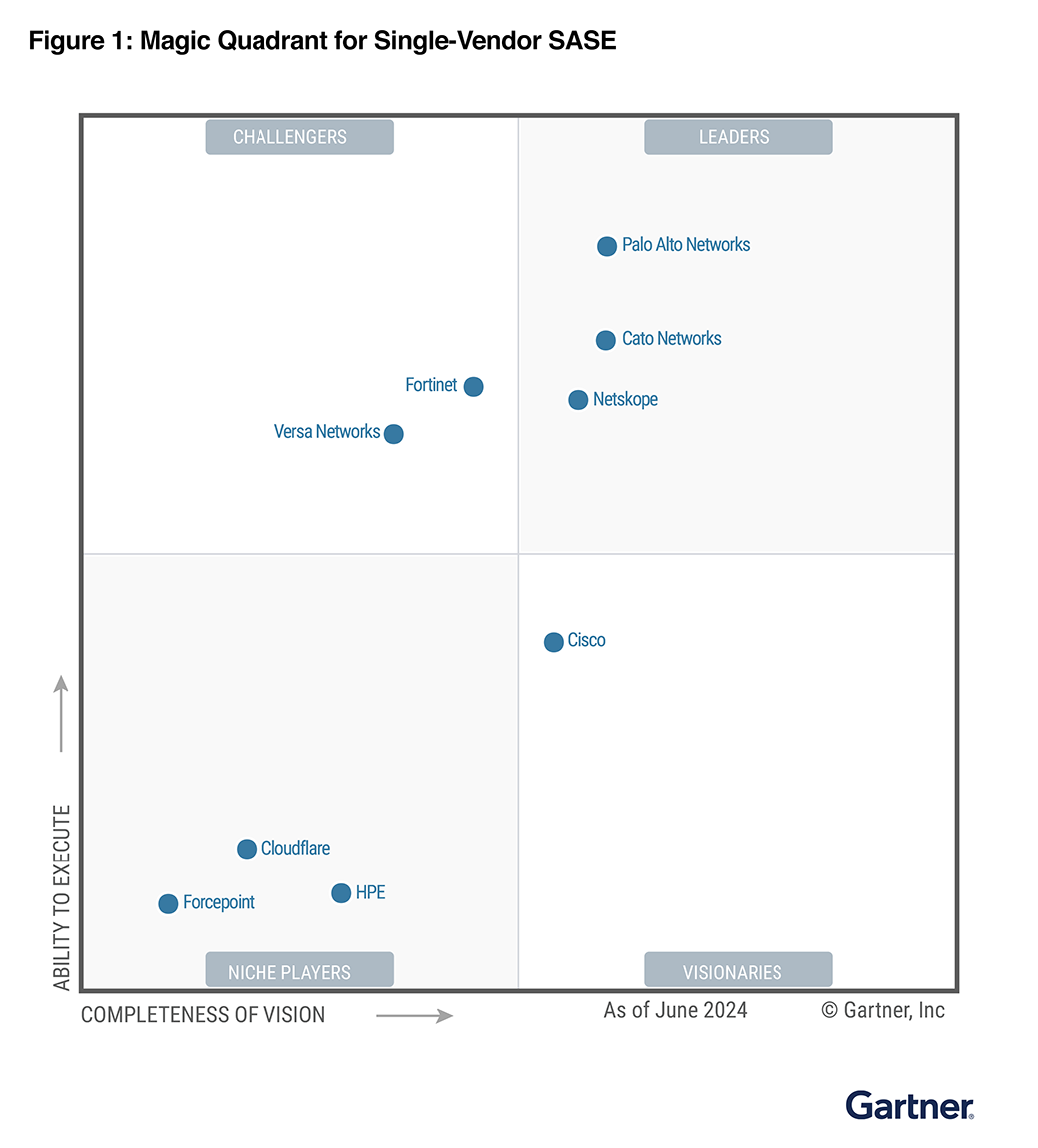
Along with the description of the selected solution include all of the key technology features, and if there are any reasons why the vendor provides additional benefits. For example, these might include if they are a Gartner Magic Quadrant leader, already implemented in other parts of the business, other products from the vendor that are currently deployed, they are a current customer, etc.
Once these core mechanics of the business case are complete then it is time to submit for review. Remember the tips provided in the article and socialize your business case with the key stakeholders and approvers well ahead of time. Let me know if my tips were useful and/or you have some you would like to add. Good luck!




 Back
Back 





















 Read the blog
Read the blog